We love a spot of fishing when we can get away for one. But “phishing”? That’s a different matter entirely.
Not that you’d ever confuse the two. One is a relaxing, intermittently exciting and always enjoyable pastime. The other is the work of criminals trying to trick you into voluntarily giving up sensitive data and information from your personal or professional lives. On the other hand, there’s no shame in mixing up phishing and “spoofing,” which is another way cyberthieves use your information for personal gain.
Whether you’re the target of phishing or spoofing, our goal is to help you recognize both and know enough to avoid biting at the lures.
Cybersecurity is Crucial
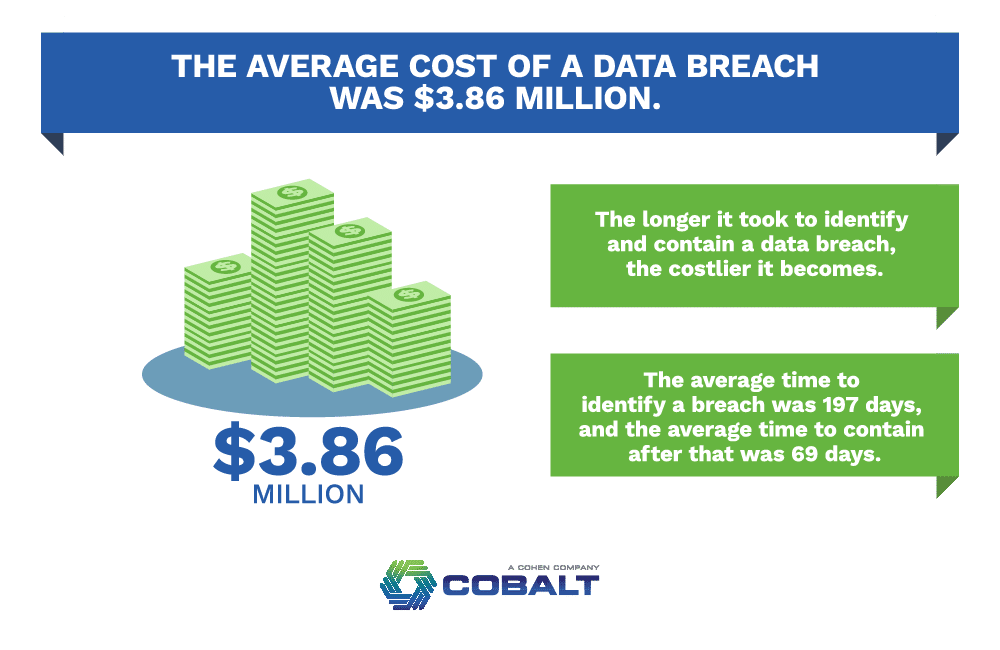
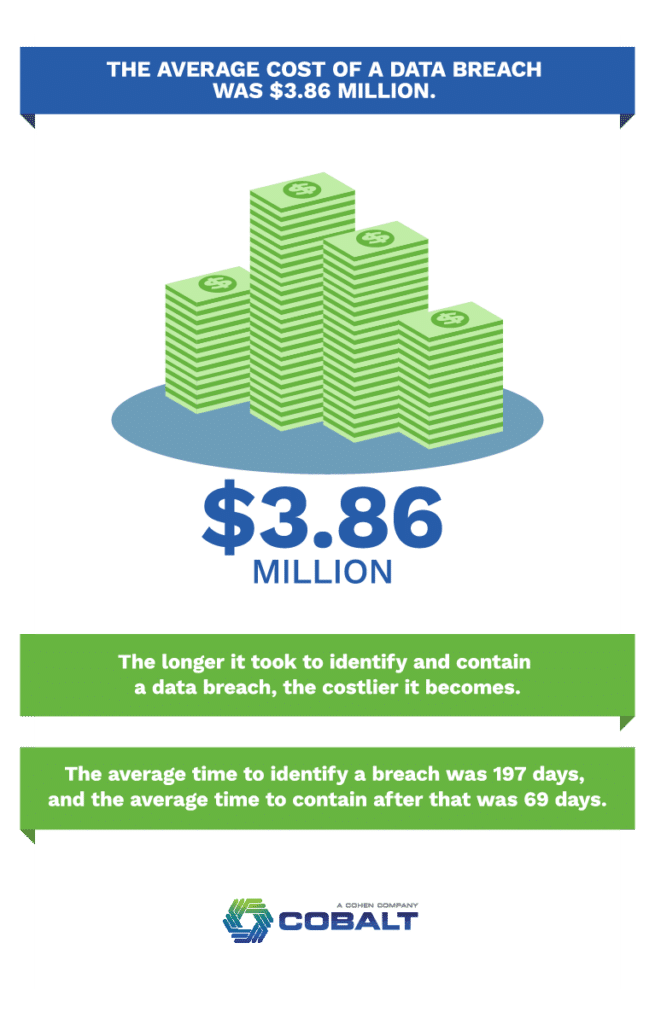
Many businesses either aren’t prepared or are underprepared for the effects of a cyberattack, which can happen very quickly and not be discovered until much later. In fact, according to a study of 2018 data breaches by Ponemon Institute for IBM Security:
- The average cost of a data breach involving 100,000 or fewer records was $3.86 million.
- The longer it took to identify and contain a data breach, the costlier it became. The average time to identify a breach was 197 days, and the average time to contain after that was 69 days.
- The vast majority of “mega breaches,” those involving of more than 1 million records, were the result of cyberattacks rather than technology glitches or human errors.
KnowBe4, a cybersecurity consultancy based in England, says more than 45 percent of data breaches in that country from 2017 to 1019 started with phishing attempts.
IT ProPortal says nearly half of all business are hit by phishing expeditions, and the larger the company the more likely it is to be attacked.
And while Tech Republic notes that financial services and tech companies are hit the hardest, any business, regardless of industry or size, can be a target.
These sobering statistics and insights underscore the importance of ensuring everyone in your business is aware of the threats and how to recognize them.
The Same, But Different
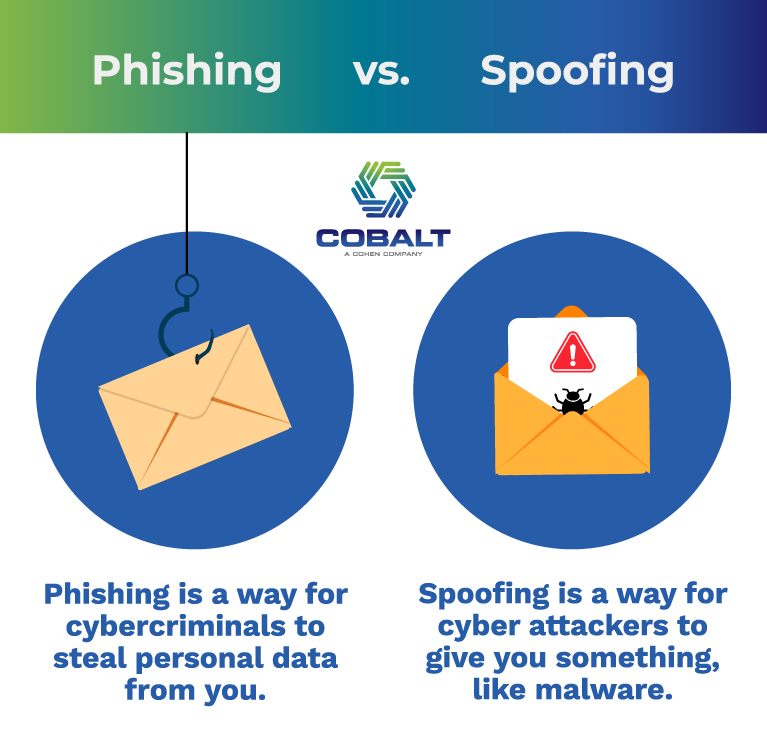
Phishing and spoofing are both cyberattacks on individuals and businesses.
People often use the terms interchangeably, but that’s not strictly accurate. It is understandable, however, given that both are ways for people with malicious intent to fool you into giving them sensitive information or downloading something that will allow them to access it themselves. Not only that, but they look similar at the front end, with official-looking communications. Hackers are skilled at creating emails and other messages that not only look legitimate, but also leverage human nature – to trust first – against us.
So what are phishing and spoofing, exactly?
What’s Phishing?
Phishing is a way for cybercriminals to get something from you, like passwords, personal identification numbers (PINs) and bank account numbers.
Cybersecurity company Malwarebytes defines phishing as “the crime of deceiving people into sharing sensitive information like passwords and credit card numbers.”
Hackers send a legitimate-looking message from a co-worker or organization your company does business with, like a financial institution, Internet service provider (ISP) or information technology (IT) consultant. Usually, the email asks you to click on a link to a bogus website where you need to provide sensitive, private or protected information to move on to the next step. If you don’t take the next step, the site warns, something horrific will happen to your company, its systems or its data.
Don’t do it!
You’d be giving away information that can lead to identity theft, massive debt your company didn’t accumulate and other serious disturbances to the business and your customers or clients.
What’s Spoofing?
Spoofing is technically a type of phishing, and many times it’s part of a broader phishing expedition. What makes it different is it’s a way for a cybercriminal to give something to you, like malware, rather than get something from you.
Malwarebytes puts it this way: “Spoofing is…the act of sending emails with false sender addresses, usually as part of a phishing attack designed to steal your information, infect your computer with malware or just ask for money.”
In a well-done spoof, the hacker creates a phony but completely legitimate-looking email from a colleague or one of your business’s service providers. The provider’s logo and color scheme are spot on, and the tone and manner of communication are perfect matches, too. Typically, the email asks you to click a link to download a file that will protect your sensitive, private or legally protected information. Again, dreadful consequences if you don’t.
Don’t do it!
Unbeknownst to you, you’d be downloading something that could jeopardize everything you’ve built and work so hard to protect.
What Can I Do About Cyberattacks?
Phishing or spoofing attacks are mostly beyond your control. Cybercriminals are going to do what they do. However, you can control the IT-based protections your business puts in place; how you prepare yourself and your employees to avoid being easy fish; and how you react when hackers cast your way.
First, your equipment:
- Make sure you have rigorous hardware and software solutions in place to protect the security of your data throughout the lifecycle of your equipment.
- Schedule cybersecurity assessments regularly to revisit risks, protocols and procedures. Conduct them every time you update or upgrade your IT assets, as well.
Next, your people:
- Train new employees as soon as possible about cyberattacks in general and how to recognize phishing and spoofing communications in particular.
- Retrain all your employees regularly.
Stop. Think. Act.
Admittedly, this isn’t very technical advice, but even in high-tech situations there are times when it pays to trust your gut.
If an email or other “official” communication brings on an uneasy feeling – Stop! Think about it. Take whatever actions are necessary to check on the authenticity of the message.
This might be as simple as calling, chatting, emailing or texting the person or organization from which the email supposedly originated. Do not use contact information from the email or text; use contact information you know already or that you obtain from a company’s website. Ask if they truly sent the communication in question. Contacting your IT department before you go any further might be warranted, and you also can contact your ISP for assistance.
Under no circumstances should you tell yourself, “Oh, I’m sure it’s nothing. I’m just being paranoid.”
In the context of cybersecurity, paranoia isn’t just a good thing, it can be a valuable thing. If something feels odd or off, there’s a good change it is.
Remember, no legitimate business or organization is ever going to ask for your social security or tax ID number through an electronic communication, and be wary of any communication requesting a bank routing or account number.
Go Ahead, Cast a Line.
Phishing, spoofing and other types of cyberattacks can be spooky stuff when it comes to the financial and operational health, security and viability of your business. But if you take a few precautions, invest in the right IT tools and keep your employees informed, you can have peace of mind – you know, like the kind you get from a real fishing trip.
* Cobalt does not necessarily endorse any of the companies mentioned or cited in this post.